Summary: In August 2025, an OAuth token compromise related to the Salesloft–Drift integration allowed attackers to access numerous Salesforce instances and extract large volumes of CRM data. More than 700 organizations are reported impacted. Between 8 and 18 August 2025, threat actors used stolen OAuth/refresh tokens from the Salesloft–Drift integration to access customer Salesforce environments. Activity included mass exports of contacts, support cases and other CRM data. Salesforce and vendors began revoking tokens and disabling the Drift integration in late August and early September 2025. Public reporting and vendor notices indicate over 700 organizations were potentially affected. Confirmed impacted organizations include: Attackers obtained OAuth tokens tied to the Salesloft–Drift integration. These tokens grant API-level access and can be used to act as authorized applications, bypassing standard user authentication. Using these tokens the adversaries: Example: Cloudflare reported internal API tokens among the data exfiltrated and rotated impacted tokens. Response and hardening steps for affected and at-risk organizations: The Salesloft–Drift incident is a stark reminder that the security posture of any organization must include strict governance over third-party integrations. Treat OAuth tokens and connected apps as critical assets: maintain inventories, enforce rotations, limit scopes, and monitor API activity. The security of an enterprise today is only as strong as its weakest SaaS integration.Salesloft–Drift Breach: Over 700 Organizations Impacted — A SaaS Supply-Chain Wake-up Call

1. Context & Timeline
2. Scope & Confirmed Victims
3. Attack Method & Data Exfiltrated
4. Why This Matters
5. Practical Recommendations
6. Conclusion
-
Outguess on Softonic
Outguess on Softonic. Outguess available…
-
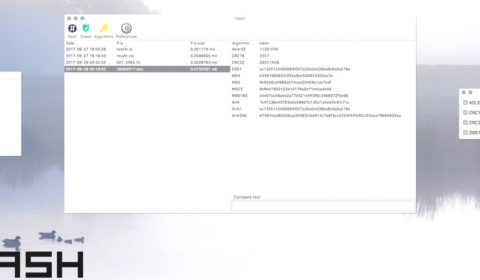
Release of Hash 1.0.5
Hash 1.0.5 has been approved…
-
Apple 1984 commercial
Apple 1984 Super Bowl commercial…
-
10.6 Souvenir
10.6 Snow Leopard Build 10A432…